DataBreaches.net was contacted by DESORDEN, who are claiming that they successfully attacked Acer India and exfiltrated 60 GB of data (they also posted their claims on a popular hacking forum).
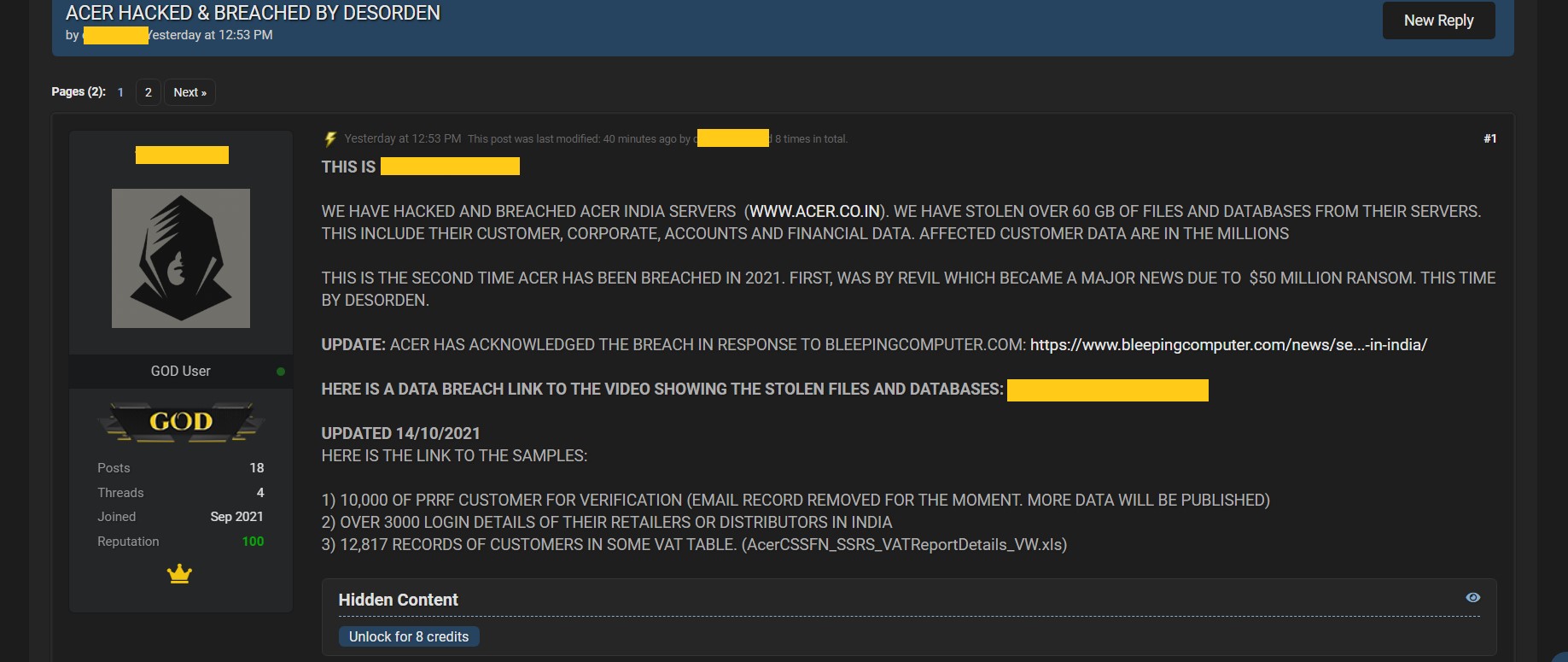
As they have done in the past, they provided a video showing directories and folders on the server they claim to have accessed. They also provided a spreadsheet with what appears to be customer information.
DataBreaches.net reached out to Acer to ask them to confirm or refute the claims, and received the following statement:
We have recently detected an isolated attack on our local after-sales service system in India. Upon detection, we immediately initiated our security protocols and conducted a full scan of our systems. We are notifying all potentially affected customers in India. The incident has been reported to local law enforcement and the Indian Computer Emergency Response Team, and has no material impact to our operations and business continuity.
As the threat actors noted, this is not the first time there has been a claimed attack on Acer. REvil ransomware operators had also claimed to have attacked them, and had started dumping data.

As this site noted, although Acer never confirmed the REvil attack or whether they paid the $50 million ransom demanded, the negotiations between the threat actors and Acer had been publicly observed. After the initial proof of claims and negotiations, REvil never did dump the Acer data.
But will Acer negotiate with DESORDEN or will they refuse to pay more ransom? We will have to wait to see.