Updated March 7, 2022: On March 6, Logansport Community School Corp. reported the incident to the Maine Attorney General’s Office as impacting 2,750 people.
Previous post:
This week, two sets of threat actors dumped data from K-12 school districts in Indiana and Oregon. Both districts had disclosed ransomware incidents in April.
Logansport Community School Corp
On April 27, Logansport Community School in Indiana reported that they were investigating how their network had been compromised by hackers on April 11. At the time, WLfi reported:
Starkey says hackers on April 11 shut down the internet and phone systems in every building in the Logansport school system, forcing the corporation to move to e-learning the next day.
A team of experts is still in-house investigating the issue.
And that was the last this site ever noticed in news.
On May 8, @RansomAlert noted that Pysa threat actors had added the school district to their dedicated leak site.
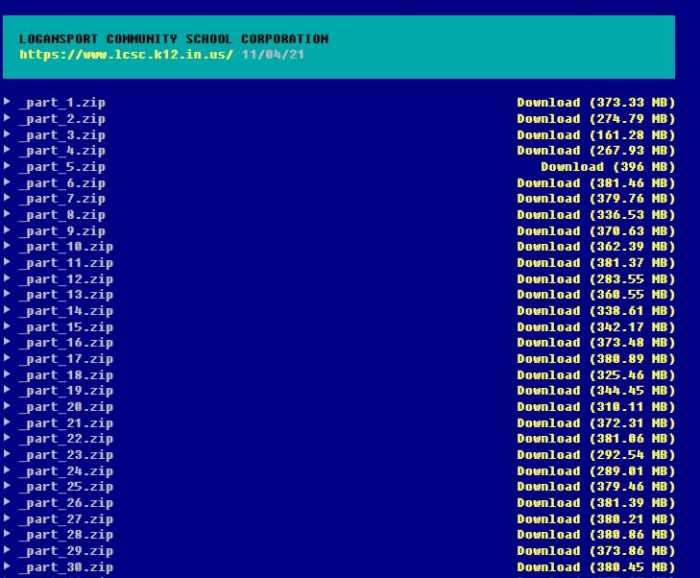
And now the threat actors have dumped data — approximately 40 GB of it. The dump consists of 140 compressed archives of files that are mostly documents. Many of the documents are old files.
While there does appear to be some possible employee personnel information files, a quick skim does not uncover any major databases such as payroll or personnel information of staff or personal information of students. Did the threat actors obtain that data and not dump it, planning to sell it, or did they not get it?
There are a number of questions here, and DataBreaches.net will update this post if more inspection of the data dump reveals more problematic files.
Centennial School District
But the Logansport data dump is not the only school district that had data dumped this week. Last month, this site also noted a ransomware attack on Centennial School District in Oregon.
Today, Babuk threat actors have dumped what they claim is 10 GB of data from the district, commenting, “Negotiations with another organization from the USA failed, it’s a shame, it’s a shame, you always try to find a workaround and not pay, but it doesn’t work”
 |
 |
Directory of folders allegedly exfiltrated by Babuk as part of incident. Redacted by DataBreaches.net.
There does not yet seem to be any notice on the school district’s web site about this newest development. DataBreaches.net may update this post after the full dump is obtained and examined.