It’s been a while since DataBreaches has seen any announcements from Desorden, but the group contacted DataBreaches over the weekend to claim responsibility for a hack and data breach of Better Way Thailand Company Limited, a personal care products and cosmetics distributor. Mistine is one of 200 companies under Saha Group, Thailand’s leading consumer products publicly listed conglomerate. Better Way Thailand Company Limited started with Mistine products.
In a statement to DataBreaches, Desorden wrote:
This data breach involved 180 GB of data and 60 GB of files, affecting more than 20 million personal data information of their customers and sales representative, which represents almost 1/3 of the entire Thailand population.
In total, DESORDEN breached into 20 of their servers, across brands of Flormar, Fairs, Friday, Mistine, MYSS, Yupin and NingNong. The data alone include customer sales representatives, employees, suppliers, export, ecommerce, corporate, HR and financial records.
Personal data alone, we have stolen over 20 million personal identifiable records, that include ID card no, birthdate, name, address ad contact detail.
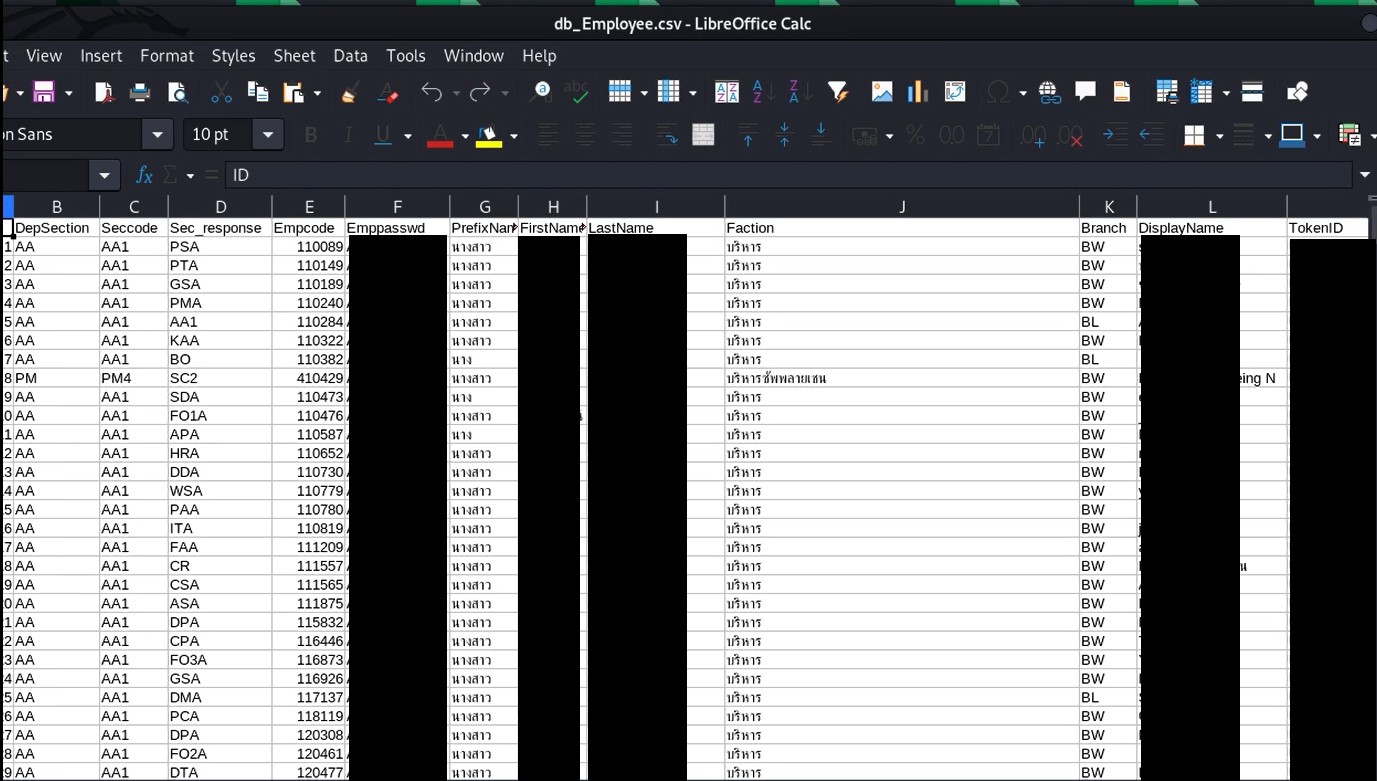
DataBreaches notes that the number of identifiable records with personal information generally does not equate to the number of unique persons who have had their personal information breached as there may be duplication across files or databases, but some of the employee and representative files DataBreaches saw each contained about 100,000 records.
Desorden informed DataBreaches that they received no reply from Mistine to their contacts or demands since July 8. As a result, they claim, they are preparing to leak and sell the data.
As has been their method, Desorden provided DataBreaches with samples from the claimed breach, including copies of what they provided to Mistine management. An mp4 file makes clear that they had access to directories and files and that those files contained personal information on employees and representatives. In a message to Mistine included in the mp4, Desorden tells them that they have deleted all the databases from Mistine’s servers after downloading copies.
DataBreaches does not know if Mistine has usable backups, but if they don’t, the loss of the files would be likely to impact functioning.
Although Desorden would not get specific about how they gained access to the servers, they stated that had exploited a few vulnerabilities that had not been patched yet.
DataBreaches attempted to contact the Data Protection Officer for Mistine via email sent to the address listed on Mistine’s site in their privacy policy. The email bounced back with error 554 5.7.1: “Recipient address rejected: Access denied.” DataBreaches re-sent the inquiry to seven email addresses found in the management .csv file provided by Desorden to this site. The seven addressess included the firm’s CEO.
Those emails did not bounce back but no reply has been received.
DataBreaches did not attempt to contact any of the employees or representatives in the sample data at this time. In the past, Desorden’s claims to DataBreaches to have hacked entities have all proven to be true, although sometimes the claims of number affected vary from the entities’ claimed number.
In the past, Desorden had posted some of the data on Raid Forums. With Raid Forums seized, they appear to have created an account on another popular hacking-related forum that has both onion and clearnet versions.
Note: Although the headline suggests Desorden was gone for a while, they claim that they have remained active the whole time but that most jobs just take months.