Tague Family Practice (TFP) in St. Louis, Missouri is a primary care practice that strives to maintain the traditional care model of a doctor who spends time getting to know you and providing preventative care as well as care for acute problems or chronic conditions.
On some date unknown to DataBreaches.net, the practice fell victim to a LockBit ransomware attack.
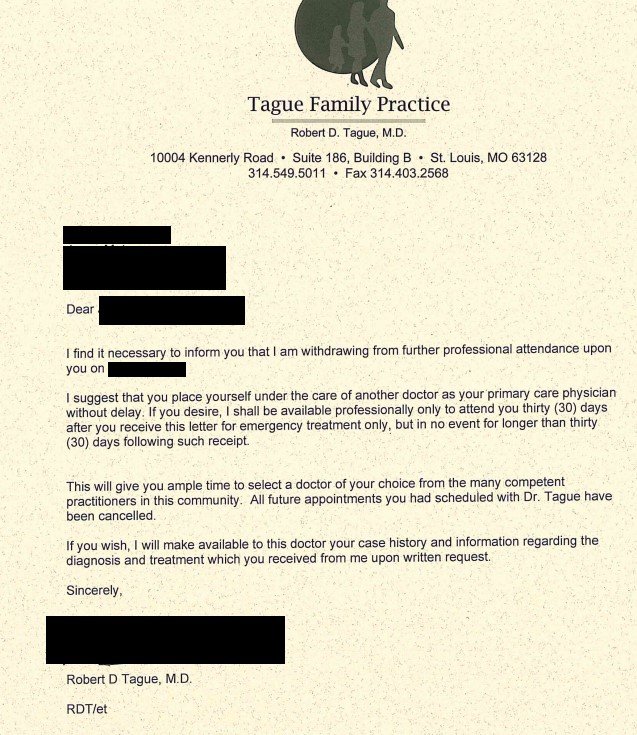
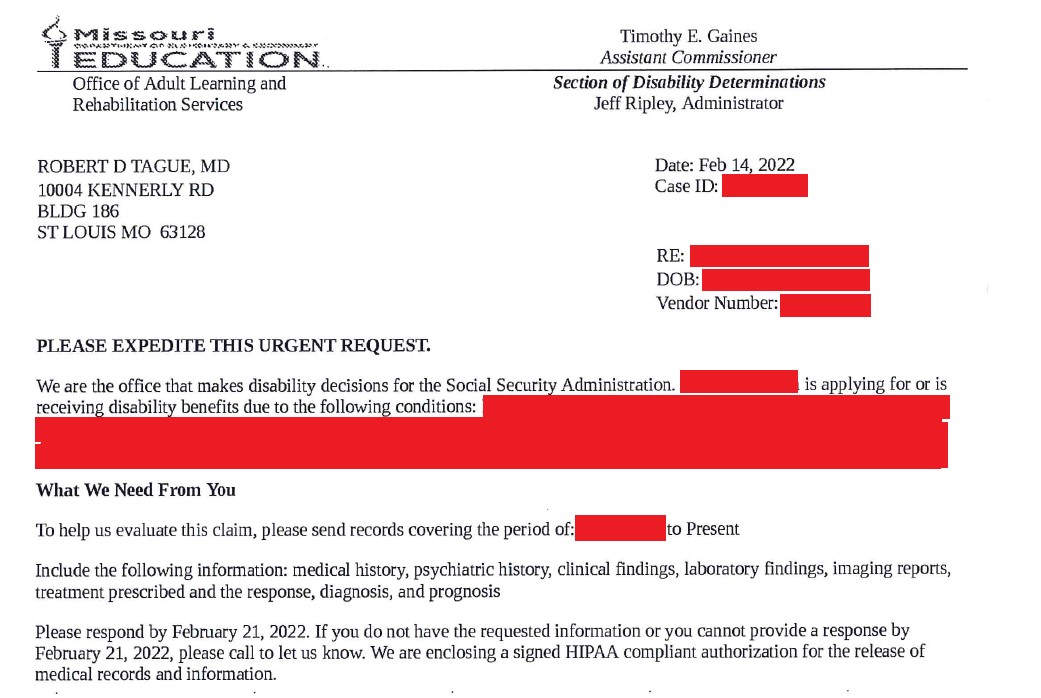
On March 17, the threat actors added TFP to their leak site. More recently, they dumped data that certainly appears to be from the practice.
DataBreaches.net did not download or examine all of the files, but sampled from some of them. The files pretty much all contained personal and protected health information, and much of it was sensitive. The dump did not seem to be of any organized EMR system, but may have been from a backup, with subfolders on billing, processed claims, labs, other patient-related records. Personal information on employees was also included, but DataBreaches.net did not see any payroll or tax records in the brief review of files.
This incident does not appear on HHS’s public breach tool at the time of this posting. DataBreaches.net does not know how many patients had their data accessed and/or acquired. The medical practice has not responded to multiple inquiries sent to it over the past three weeks. As one consequence, DataBreaches.net does not know whether the practice has sent any notification letters to patients and to what extent the practice might have been impacted by any file encryption or corruption. There is nothing on the practice’s website to suggest that there had been any interruption in services.
This post may be updated when more information becomes available.
If you are a patient of Tague Family Practice, please contact this site to let us know if you have received any notification of a data security incident affecting your information.