The HBO hackers apparently want us all to know that they weren’t bluffing when they said they would not play games or go along with delaying tactics.
In a letter to HBO, described previously on this site, the hackers had written, “As we witnessed in other cases, Fucking FBI or other police enforcements, teach you couple of outdated trick to play with us and buy time. It doesn’t work with us.”
Those tricks apparently include promising to pay a large bug bounty but not paying the demanded ransom amount by the actual deadline.
Today, the hackers contacted DataBreaches.net and a few other media/news outlets with a new link to the previously dumped files. But “Mr. Smith” also attached a file labeled as “HBO’s Response.”
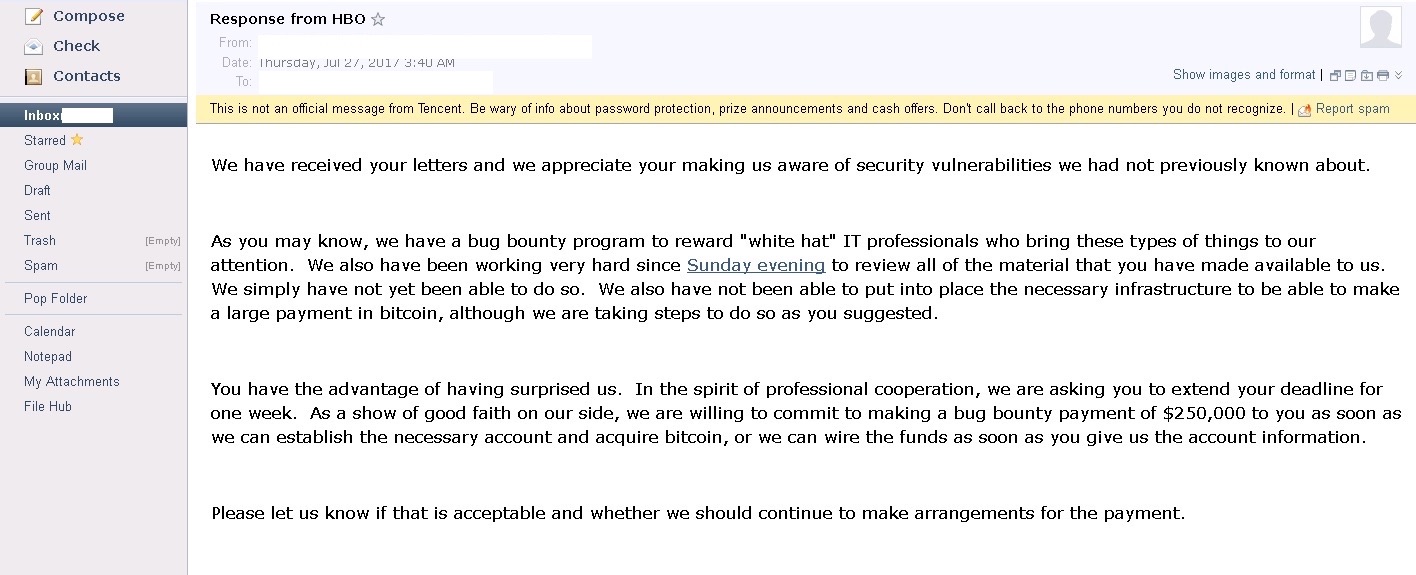
The file, which DataBreaches.net is redacting to delete the HBO executive’s name and email address, is dated July 27, and acknowledges receiving the hackers’ letters. The letter is not from Richard Plepler, HBO’s CEO. In other communications, the hackers indicated that they would only correspond with him going forward.
Trying to frame – or re-frame – the situation as a bug bounty possibility, HBO asked the hackers to extend their deadline for payment and committed – “as a show of good faith” – to making a bug bounty payment of $250,000.00.
HBO was asked to confirm whether the email was authentic, but DataBreaches.net has received no statement as yet. This post will be updated if and when one is received.
That said, in light of data leaks we’ve seen and the fact that the hackers sought 6-months of their annual income (which they estimated at $12-15 million), it appears that the hackers did not find $250,000 acceptable at all.
Update: It’s been pointed out to me that the hackers may not have believed the offer was genuine and may have viewed it simply as a delaying trick. It would be nice to hear from the hackers with a statement as to how they interpreted the offer, so I’ve sent an email inquiry and hope they’ll respond.
AS soon as they get the money, it will be recorded..
WHERE and WHEN..
As soon as they TRY to use the money, it will be traced..
Closer and closer the net will be..
They are taking TIME, to set things up..
Unless you are Very very, Good and know the OLD internet VERY WELL..and how it really works..
they wont have a chance, after a time..