On May 6 and May 7, DataBreaches reported that the attack on Murfreesboro Medical Clinic & SurgiCenter (“MMC”) appeared to be the work of the ransomware group known as BianLian.
On June 14, MMC issued an updated notice on their website, as noted by Daily News Journal. The news report reiterated that MMC refused to pay the ransom or contact the threat actors at all — as a matter of principle, according to the CEO of the for-profit center.
MMC’s investigation was “unable to determine whether any personal information was actually accessed or removed from our network,” the June 14 notice stated. Perhaps if they had contacted the attackers, they would have found out what data the bad actors had accessed or acquired?
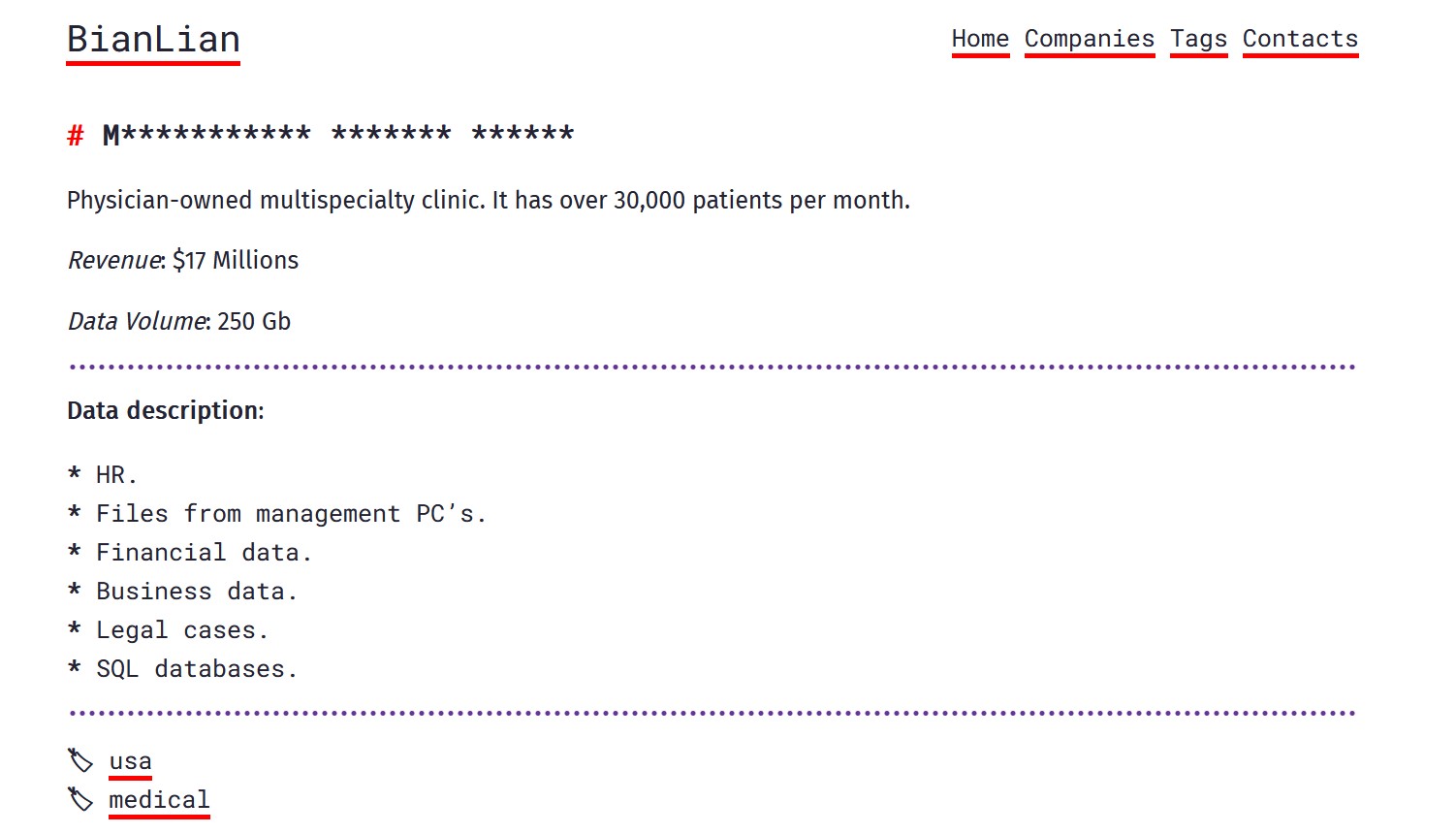
MMC was listed on BianLain’s leak site in asterisked form, which is one of the things that particular group does to try to pressure victims into paying. At some point, BianLian never fully named MMC on its site, and the listing silently disappeared. Often a listing disappears due to the victim paying the extortion demand. But MMF insisted it did not pay any ransom, so what is the explanation? BianLian had claimed to have 250 GB of files.
On June 21, MMF notified HHS that 559,000 patients were affected.
Update July 11, 2023: As previously reported by DataBreaches, it appeared that MMC was a victim of an attack by BianLian, but the listing was removed silently at some point. Today, BianLian re-listed it without any asterisks to mask the name. Why it was ever removed is a bit of a mystery, but now a multi-part leak is listed with the original claim of 250 GB of data. As if often the case with these threat actors, attempts to download the leak parts failed when tried today.