Grand Street Medical Associates is a multi-disciplinary practice in Kingston, New York. At some point, what appears to be a vast amount of their patients’ protected health information was left exposed on an unsecured FTP server. The leak was discovered by a security researcher, who notified GSMA and then contacted DataBreaches.net on March 12.
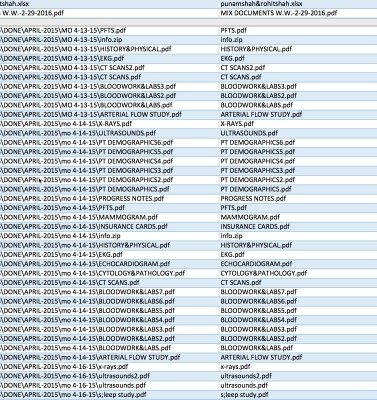
According to data provided by the researcher and reviewed by DataBreaches.net, there were over 14,600 files and more than 20GB of data. Each file that we skimmed contained PHI on multiple patients. It appeared that the files were part of an effort to scan and digitize paper records from patients seen since December, 2011.
Dozens of files were labeled “patient demographics.” DataBreaches.net randomly selected one such file analyze the contents and found that it contained PHI on approximately 65 unique patients. For most of those patients, there was a new patient form that asked the patient whether they had had any recent bloodwork or labs, whether they had had any testing done, and whether they had had any recent hospitalization. The new patient forms also required the patient to provide their:
- name
- marital status
- date of birth
- age
- gender
- phone numbers (home) and (work)
- street address, city, state, zip
- occupation/employer
- spouse’s name & occupation
- emergency contact (other than spouse)
- SSN
- Insurance & billing info
Approximately 40 of the 65 patients provided the requested SSN. Sixty patients provided their insurance information. For many patients, there were also photocopies of their insurance cards and driver’s licenses.
The new patient forms also included space for the patient’s signature on a HIPAA release form, and all patients in that particular file had signed the form, so their signatures were also caught up in the exposure.
In addition to the patients’ information, there was PII for friends or family members. When a family member was the subscriber to an insurance plan, their PII was also provided.
And that was just one of the “patient demographic” files. Other files appeared to batch patient medical information such as lab tests, consultations, progress notes on patients (172 files), consultations with hospitals, and insurance information.
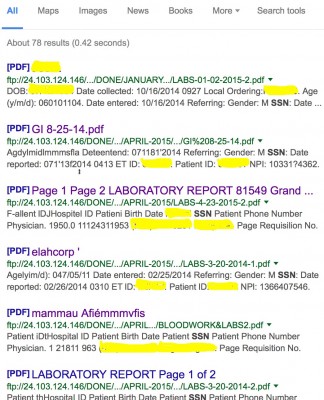
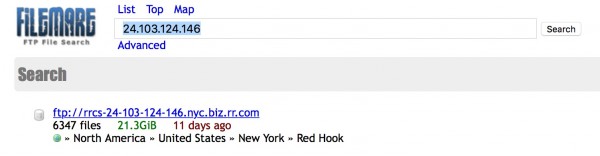
To make matters worse, dozens of the more than 14,000 files were indexed by Google, while Filemare indexed over 6,300 files.
Grand Street Medical Associates did not respond to two emailed inquiries asking how many patients had PHI in the exposed files, for how long their records were exposed, and how it happened (i.e., was any vendor or BA involved). Nor does DataBreaches.net know how many times the files may have been accessed or downloaded.
At this point, DataBreaches.net does not know whether GSMA intends to notify its patients and/or HHS, but such exposure put thousands of patients at risk of identity theft and medical identity theft, as well as the risk of having sensitive medical information shared broadly. If the data weren’t acquired by bad actors or misused, everyone can count their lucky stars.
DataBreaches.net delayed publication of this incident until the files were secured and cache cleared, as the files indexed by Google sometimes revealed the patients’ names, dates of birth, and other details.
This post will be updated if more information becomes available. Hopefully, GSMA will issue a statement that explains what happened and whether or not the files were accessed while they were exposed.
If you were or are a patient at GSMA, please contact this site to let me know if you have been contacted by GSMA about the incident.
CORRECTION: This post was corrected post-publication as an earlier version indicated that there were 172 “patient demographics” files. That should have read “progress notes” files. There were 70 patient demographics files.