At some time before or in early October, the Everest Ransom Team hacked Rundle Eye Care in California. On January 11, Drs. Keith and Herman Rundle notified patients and the California Attorney General’s Office about the incident.
In their notification, the doctors do not reveal precise dates of the attack or its discovery but claim that they recently
detected and stopped a network security incident. An unauthorized third party temporarily gained access to our network environment. Although we have found no evidence that your information has been specifically misused as a result of the incident, an investigation revealed that the following categories of your information which may have been exposed: name, date of birth, and treatment information.
Their notification to patients is dated approximately three months after the attack. And although the notification claims patient data “may have been exposed,” it does not tell patients their data was actually stolen and leaked publicly back in October.
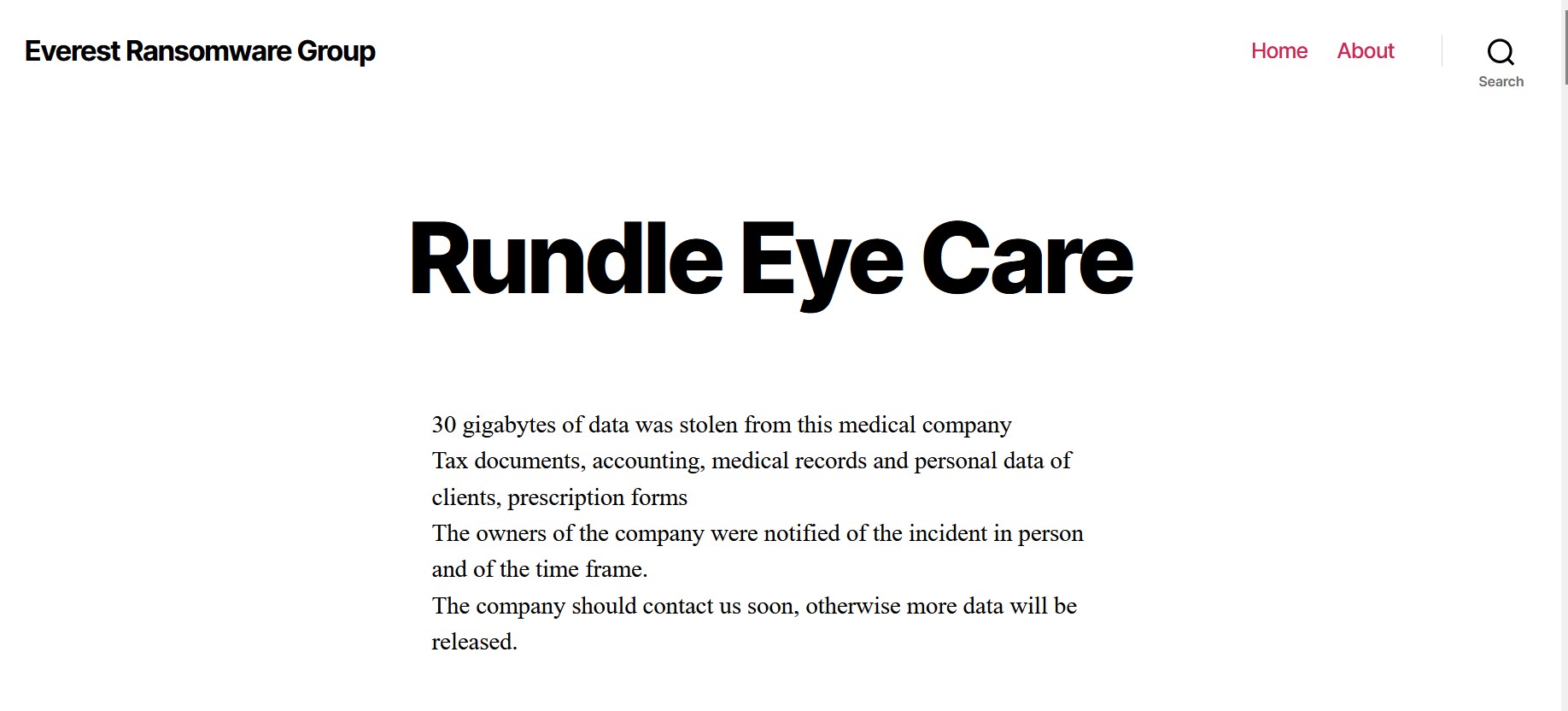
Everest’s listing on its leak site in early October claimed they acquired 30 GB of data from Rundle, including patient information. The listing also stated, “The owners of the company were notified of the incident in person and of the time frame. The company should contact us soon, otherwise more data will be released.”
According to Everest, then, the doctors knew back in October that the incident involved more than just exposure.
Whether Rundle’s physicians ever contacted Everest or not is unknown to DataBreaches, but on October 25, Everest leaked 20 GB of data on a well-known hacking forum accessible on the clear net and the dark web.

As of publication, there is no listing for this incident on HHS’s public breach tool and the total number of patients affected is unknown.
DataBreaches reached out to Everest Team to ask whether they had encrypted any of the files (they usually do not encrypt) and whether they had leaked all of the data they had exfiltrated. This post will be updated when a reply is received.
Update: On February 3, this incident was added to HHS’s breach tool with a submission date of January 12, 2023. The doctors reported that 7,528 patients were affected.