We also stop all activity versus all kinds of medical organizations until the stabilization of the situation with virus — Maze Team, March 18, 2020
Despite having proclaimed that they would not be attacking medical entities during the pandemic, Maze Team has attacked another medical entity: a Bellevue, Washington-based plastic surgeon who specializes in surgery of the eye and facial areas. Dr. Kristin Tarbet’s website does not provide any notice or indication of trouble, but Maze claims to have successfully attacked them on May 1, and offers plenty of proof of attack.
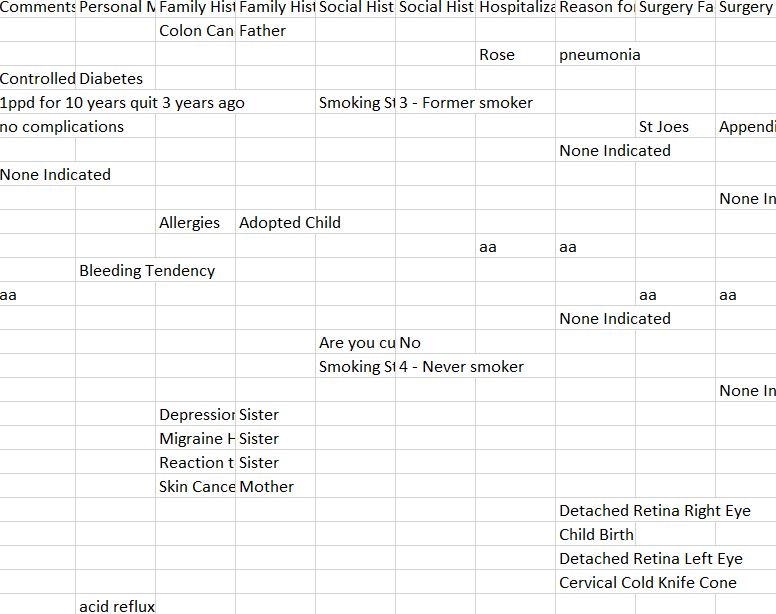
As part of its proof, Maze dumped a number of files with protected health information. One spread sheet for patient appointments contained approximately 39000 entries. A small number of entries were test data, but the rest appeared to be real data, where there might be multiple entries/rows for any one patient. For each patient, there was a first name and last name, date of birth, date of appointment, type of appointment, purpose of appointment, length of appointment, and any comment. Patient addresses, phone numbers, and insurance information were not included in this particular spreadsheet, but were included in other spreadsheets that also contained patients’ email addresses, home and mobile numbers, and for some patients, Social Security numbers. Yet other files contained specific medical information such as diagnostic codes, treatment codes, complaints, allergies, and medications that the patient was on, height, weight, blood pressure, respiration rate, and other notes. And yet another file contained insurance information.
From the patients file alone, it would appear that Dr. Tarbet might have at least almost 22,000 patients to notify of this breach, and possibly many more.
In addition to files that contained “Patient” in their filename, there was a file containing important password information for Quickbooks and for their wireless merchant credit card account. There were also other corporate-related files, but frankly, it’s the protected health information that is the most concerning. Perhaps Maze Team dumped this as a warning that they would dump insurance or credit card information or pre- and post-surgical pictures of identifiable patients, but if I was a patient, I’d be more concerned about the PHI that they have now already revealed.
DataBreaches.net attempted to reach Dr. Tarbet for a statement about the incident but was unable to get a response by publication time. This post may be updated if more information becomes available.