A criminal complaint was unsealed today in federal court in Brooklyn charging Sagar Steven Singh and Nicholas Ceraolo with wire fraud and conspiracy to commit computer intrusions. The charges stem from Singh’s and Ceraolo’s efforts to extort victims by threatening to release their personal information online. Singh was arrested this morning in Pawtucket, Rhode Island, and will make his initial appearance this afternoon in federal court in Providence, Rhode Island. Ceraolo remains at large.
In pursuit of victims’ personal information, Singh and Ceraolo unlawfully used a police officer’s stolen password to access a restricted database maintained by a federal law enforcement agency that contains (among other data) detailed, nonpublic records of narcotics and currency seizures, as well as law enforcement intelligence reports. Ceraolo (with Singh’s knowledge) also accessed without authorization the email account of a foreign law enforcement officer, and used it to defraud social media companies by making purported emergency requests for information about the companies’ users.
Breon Peace, United States Attorney for the Eastern District of New York, and Ivan J. Arvelo, Special Agent-in-Charge, Homeland Security Investigations, New York (HSI), announced the charges.
“Singh and Ceraolo aptly belonged to a group called, as their crime was, ‘Vile.’ That conduct ends today,” stated United States Attorney Peace. “As alleged, the defendants shamed, intimidated and extorted others online. This Office will not tolerate those who impersonate law enforcement officers and misuse the public safety infrastructure that exists to protect our citizens.”
“As these charges make clear, the alleged unauthorized access of a US federal law enforcement system and impersonation of law enforcement officials are serious offenses, and the criminals who perpetrate these schemes will be held accountable for their crimes.” stated HSI New York Special Agent-in-Charge Arvelo. “HSI and its law enforcement partners are committed to safeguarding public safety infrastructure from cyber criminals and ensuring that those seeking to compromise these systems face the fullest extent of the law.”
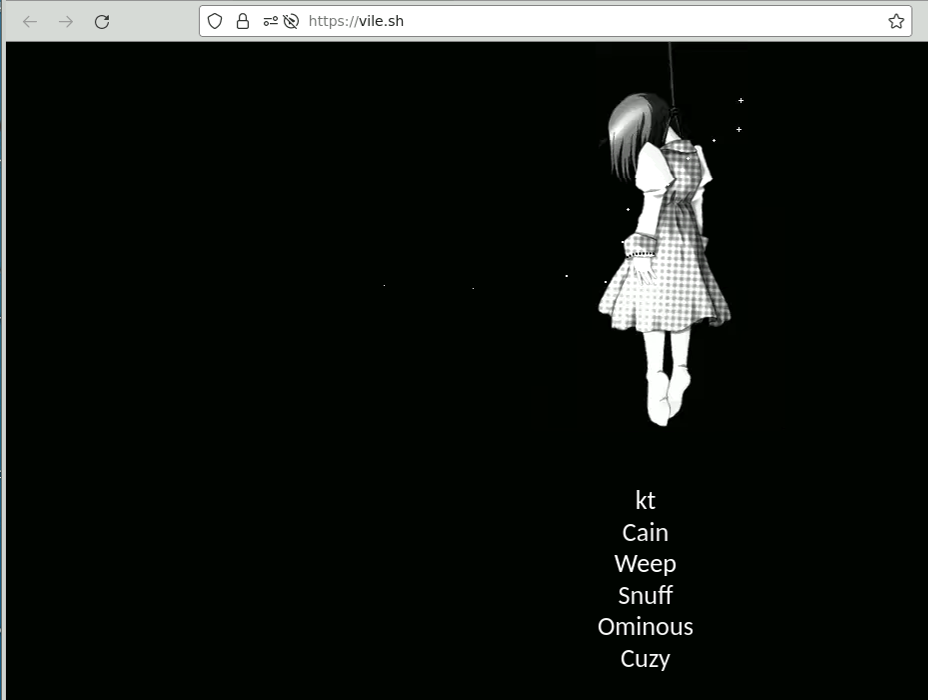
As alleged in the criminal complaint, Singh and Ceraolo belonged to a group called “ViLE,” whose logo is the body of a hanging girl, as depicted below in the group’s official roster:
Members of ViLE sought to collect victims’ personal information, such as names, physical addresses, telephone numbers, social security numbers and email addresses. ViLE then posted that information (or threatened to post it) on a public website administered by a ViLE member – an action known as “doxxing.” Victims could pay to have their information removed from or kept off the website.
ViLE members acquired victims’ information by various means, including by impersonating law enforcement officers and sending forged requests or orders purporting to be from law enforcement to social media companies, often demanding victim information on the pretense that loss of life was imminent.
As alleged in the complaint, in pursuit of victims’ personal information. Singh and Ceraolo used a police officer’s credentials to access without authorization a nonpublic, password-protected web portal (the “Portal”) maintained by a U.S. federal law enforcement agency, whose purpose is to share intelligence from government databases with state and local law enforcement agencies. After both Singh and Ceraolo accessed the Portal, Ceraolo wrote to Singh: “were all gonna get raided one of these days i swear.” Later that day, Singh wrote to a contact that the “portal [] i accessed i was not supposed to be there not one bit.” Singh said he had “jacked into a police officer’s account” and “that portal had some fucking potent tools.” Singh continued: “it gave me access to gov databases,” followed by the names of five search tools accessible through the Portal.
Within one day of this unauthorized access, Singh was using his access to the Portal to extort victims. Singh wrote to a victim (Victim-1) that he would “harm” Victim-1’s family unless Victim-1 gave Singh the credentials for Victim-1’s Instagram accounts – and appended Victim-1’s social security number, driver’s license number, home address, and other personal details. During the conversation, Singh told Victim-1 that he had “access to [] databases, which are federal, through [the] portal, i can request information on anyone in the US doesn’t matter who, nobody is safe.” Singh added: “you’re gonna comply to me if you don’t want anything negative to happen to your parents.” Singh ultimately directed Victim-1 to sell Victim-1’s accounts and give the proceeds to Singh.
In addition to accessing the Portal without authorization, Ceraolo posed as a police officer to obtain subscriber information from various online service providers. For example, between February 2022 and May 2022, Ceraolo accessed without authorization an official email account belonging to a Bangladeshi police official. Ceraolo used the account to pose as a Bangladeshi police officer in communication with U.S.-based social media platforms. In one instance, Ceraolo induced a social media platform (Platform-1) to provide information about one of its subscribers, including the subscriber’s address, email address and telephone number, by asserting that the subscriber had participated in “child extortion” and blackmail and had threatened officials of the Bangladeshi government. Ceraolo shared the information with another ViLE member, who sent the information to Singh. Ceraolo also used the Bangladeshi police account to attempt to purchase a license from a facial recognition company whose services are not available to the general public.
Similarly, between March 2022 and May 2022, Ceraolo targeted a company (Platform-2) that operates an online gaming platform. Ceraolo used the Bangladeshi police account to request data about one of Platform-2’s users. Employees of Platform-2 detected Ceraolo’s fraud and publicly discussed the attempted fraud. Ceraolo told an associate that he would “hack” Platform-2 in retaliation for “acting like their [sic] untouchable,” that he would “handle dumping and defacing everything for trying to snitch to homeland security” and that he could “easily get 6 figs” for selling Platform-2’s information “on one of the dark web markets.” At Ceraolo’s behest, an associate posed as a U.S. local police officer and sent a forged subpoena to one of Platform-2’s vendors, seeking registration details about Platform-2’s administrators. The vendor did not provide the information.
If convicted, Ceraolo faces up to 20 years’ imprisonment for conspiracy to commit wire fraud, and both Ceraolo and Singh face five years’ imprisonment for conspiracy to commit computer intrusions. The charges in the complaint are allegations, and the defendants are presumed innocent unless and until proven guilty.
The Office extends its appreciation the New York City Police Department and the Federal Bureau of Investigation for their assistance on this case.
The government’s case is being handled by the Office’s National Security and Cybercrime Section. Assistant United States Attorneys Alexander Mindlin, Ellen Sise and Adam Amir are in charge of the prosecution.
The Defendants:
NICHOLAS CERAOLO (also known as “Convict,” “Anon” and “Ominous”)
Age: 25
Queens, New York
SAGAR STEVEN SINGH (also known as “Weep”)
Age: 19
Pawtucket, Rhode Island
E.D.N.Y. Docket No. 23-MJ-213
Source: U.S. Attorney’s Office, Eastern District of New York